Infected third-party software key driver for cryptojacking on the Internet
According to the ENISA threat landscape report, one of the emerging cyber threats over the past year is cryptojacking. In cryptojacking, attackers make use of your PC to mine cryptocurrency for them while you browse the web and visit an infected website. As the mining happens within your web browser, the attack can be launched in the background even without you installing any malware.
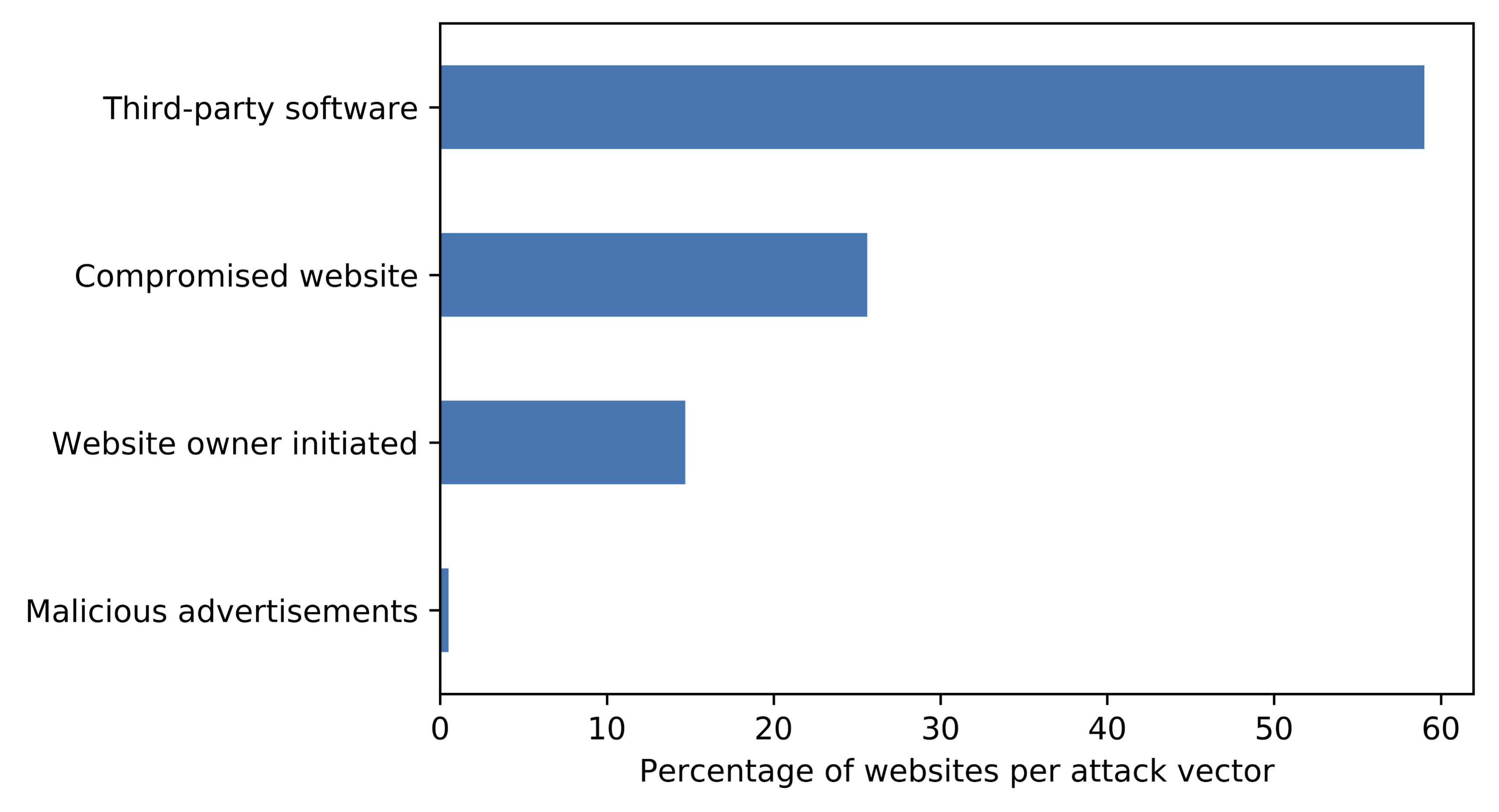
In a longitudinal study of 55 million websites, we investigated how actors spread these infections, organize their activities and monetize cryptojacking on the Internet. We find indications of attempted cryptojacking on more than 20,000 websits, although during our study period in late 2018 and early 2019, only 10,100 of them were actively mining on their visitors' PCs. As cryptojacking is built based on WebAssembly and Javascript, we can efficiently analyze the Javascript source code to study how the attacker has configured their setup or where the infection is placed into the website. Through an automatic stack trace analysis and after manual and automatic de-obfuscation, we found that webmasters installing cryptomining themselves in less than 15% of the cases, and also hacks of websites to install miners only accounts for a quarter of all activity.
How cryptojacking actually spreads is by means of compromised third-party software, for example malicious plugins to popular content management systems such as Wordpress, externally hosted libraries such as jquery, as well as malicious code in (pirated) website templates that people download from the Internet. Clever criminals have hidden malicious mining code deeply in many of these, and unsuspecting website owners thus let all of their visitors mine for the criminals' profit. About half of the compromises are driven in orchestrated activity organized in more than 200 campaigns, where the largest actors have about 1000 websites under their control.
To learn more, read the full report or an extended abstract.